API Security and Threat Prevention Guide
Strong security is necessary to implement and expose API publicly. Cloud-native apps are strengthened by CNAPP platforms which rely on industry-standard protocols to secure APIs. This blogs covers an array of cloud-native security solutions guarantees end-to-end protection, compliance, and resistance against the top API vulnerabilities identified by OWASP.
Reading Time: 7 minutes
Table of Contents
Application programming interfaces (APIs) are the foundation of almost all modern programs. APIs are useful because they make data sharing and communication with external systems simpler. The use of APIs has increased exponentially as a result of cloud computing’s widespread adoption. Because of this, API security is becoming a top priority for organizations. API security must be given top priority as a fundamental precaution for safeguarding cloud-based services. They serve as the main entry point through which hackers might take advantage of weaknesses in cloud-based systems.
As to Gartner’s prediction, since 2022, APIs have emerged as the primary attack vector. Businesses that depend on microservices and cloud-native apps can’t ignore it. Static and runtime protection are areas in which cloud-native application protection platforms (CNAPP) thrive. However, it’s too soon to say whether or not they can be applied to the particular problems that APIs provide. This blog examines the many aspects of API security and the features that enhance CNAPP. Upon completion, you will possess practical advice and tactics to counteract cyberattacks that aim to compromise cloud-native and API-based services.
The need for API security is highlighted by the 2017 Equifax data breach, in which hackers used an API vulnerability to get sensitive personal data belonging to about 147 million individuals. Because APIs are widely utilized in the banking industry for account management and transactions, hackers looking to steal financial data often target these platforms. Because healthcare companies depend on APIs to transfer patient data across various systems, strong API security is essential to safeguarding private medical data. API security is about more than just data protection—it’s about preserving your company’s integrity and credibility.
- PII Protection – Attackers can use APIs to expose private information to outside systems. The usual target is organizations with sensitive financial, medical, or other data. APIs can also leak personally identifiable information (PII).
- Cybersecurity Mitigation – Strong security measures are necessary as API weaknesses are exploited by cybercriminals. Securing APIs lowers the risk of cyberattacks and improves cloud security posture. 88% of organizations experience issues with API authentication.
- Compliance and audit readiness – API security is crucial for industries adhering to regulatory compliance requirements. All guidelines like HIPAA, PCI-DSS, and GDPR require it.
- Reputation and trust – Fortifying APIs eliminates the chances of data breaches and vulnerabilities in cloud-native apps. It protects the company’s brand and builds client confidence.
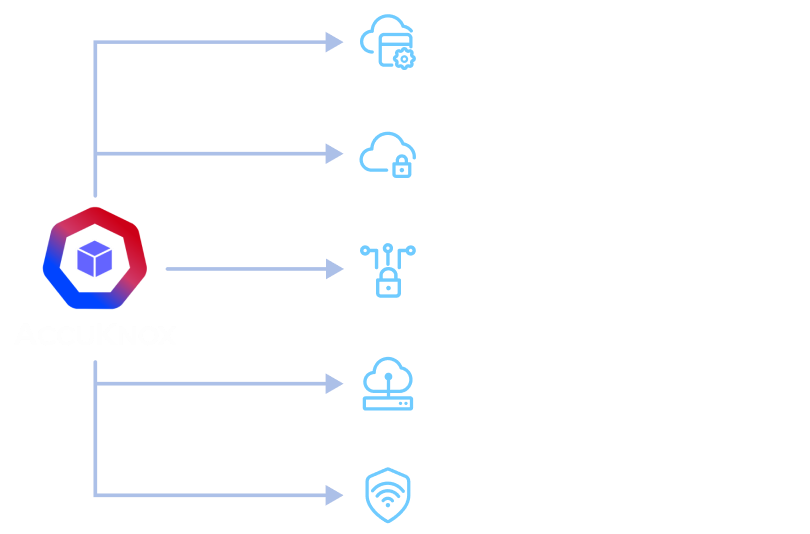
Cloud-native apps looking to safeguard their APIs should make use of tools provided by a CNAPP platform.

Key Measures for API Security
APIs function as the conduits for data flow within cloud-based applications and services. They act as intermediaries between applications, facilitating seamless communication and data exchange. Moreover, APIs grant access to critical services and functionalities within your cloud-based applications. When an attacker manages to compromise APIs, they get around security measures. Access is bypassed to your cloud-based services without authorization. Data breaches, monetary losses, and reputational harm are common headlines. APIs are one of the most lucrative targets accessible today for malicious actors.
- Authenticity and authorization Authentication ensures that only authorized users access APIs, while authorization controls their actions. Implementing robust authentication and authorization mechanisms is vital for safeguarding cloud-based applications.
- Encryption. SSL/TLS encryption for APIs is fundamental to ensuring the secure transmission of data. It prevents nefarious entities from potentially intercepting data.
- Inventory Control. Precise API inventory is essential but difficult since cloud services are dynamic. API traffic and use are tracked by logging, monitoring, and discovery. Especially with runtime capabilities that are always active,
- Protection at Run-Time. API run-time security defends against a range of threats, such as DDoS, brute force, and BOLA assaults. Customized rules and checks prevent API calls that try to violate business logic. Brute force and DoS assaults are lessened by rate restrictions and throttling.

Source: https://salt.security/api-security-trends
Finance
- Token-based authentication and authorization via protocols like OAuth 2.0 are used by secure APIs in banking and financial services.
- Banks encrypt their APIs with OAuth 2.0, enabling users to access financial data via mobile apps.
- After user authentication, access tokens are granted, enabling safe and regulated access to private information.
Healthcare
- Encryption methods are used to safeguard patient records accessible via APIs.
- Transport Layer Security (TLS) can be used to encrypt data transmitted when an electronic health record (EHR) system and a healthcare provider’s system connect via an API.
- Only authorized healthcare workers may access patient information via APIs thanks to authentication and authorization techniques including role-based access, access restrictions, and API keys.
41% of firms claim that controls and visibility over security are lacking in development processes.

Source: OWASP Top 10 API Security Risks
Advantages of CNAPP
| Aspect | Benefit |
| Comprehensive Security | CNAPP provides runtime protection, vulnerability management, threat detection, and response capabilities, addressing web application attacks, API attacks, and cloud infrastructure threats |
| Integration of Cloud Security Categories | CNAPP combines multiple cloud security categories, such as DevSecOps, CSPM, IaC scanning, KSPM, CIEM, and CWPP, streamlining security efforts. |
| Full-stack Application Visibility | SecOps and DevOps teams benefit from enhanced visibility, facilitating efficient threat detection and response. |
| Automated Vulnerability Management | Automated detection of vulnerabilities in API code and configurations. Offers remediation recommendations based on baselines. |
| API Security | Validation and monitoring of API traffic. Guarantees secure communication between application components |
| Identity and Access Management | CNAPP manages user access enforces role-based access control,and ensures secure authentication. |
| Compliance and Audit | The platform aids in maintaining regulatory compliance by continuously monitoring the environment and generating audit reports. |
Components of CNAPP and Their Functions
| Component | Function |
| Policy Engine | Enforces security policies, ensuring compliance with best practices. |
| Runtime Protection | Monitors application behavior in real-time to detect and block suspicious activities. |
| Vulnerability Management | Scans for potential vulnerabilities in application code, containers, and infrastructure, providing remediation recommendations. |
| API Security | Validates and monitors API traffic for secure communication. |
| Identity and Access Management (IAM) | Manages user access, enforcing role-based access control and secure authentication. |
| Compliance and Audit | Aid in maintaining regulatory compliance by continuously monitoring the environment and generating audit reports. |
API Protection Capabilities that Enhance CNAPP
Real-time Threat Detection and Mitigation
- API protection solutions ensure high efficacy rates in real-time threat detection. They identify and mitigate malicious traffic to maintain uninterrupted, business-critical transactions.
- These solutions are designed to prevent false positives that disrupt operations.
- Real-time threat detection aligns with cloud workload protection platforms (CWPP) and container network access and policy solutions. Constant vigilance against cyber threats targeting accessible applications is virtually guaranteed.
Shadow API Discovery
- Unidentified APIs used by internal groups without security team notification pose a threat to organizations.
- Shadow API discovery complements CNAPP by safeguarding against unknown APIs and cloud components. CNAPP focuses on known applications and infrastructure. This capability extends protection to the realm of the unknown.
Rapid Application Code Changes
- Cloud-deployed API applications almost always follow agile development methodologies. API specifications are changed; hence, they need to be QA’ed with security in mind.
- Unmonitored changes can lead to compliance breaches and data exposure issues.
- Seek out and address the OWASP API Security Top 10 vulnerabilities.
- Regulated inventory checks are also provided to identify and mitigate such vulnerabilities before they can be exploited.
When addressing API security, a comprehensive approach should encompass the six stages of the continuous API lifecycle, aligning effectively with CNAPP.
| Stage | Description |
| Discovery | Continuous discovery of an organization’s API attack surface, including shadow APIs implemented without security oversight. |
| Inventory | Management of both managed and unmanaged APIs from a centralized location. |
| Compliance | Ensuring API compliance with organizational security policies and industry best practices. Notifications for non-compliant APIs facilitate immediate remediation. |
| Detection | Real-time detection of API threats with minimal false positives, eliminating the need for third-party tools. |
| Prevention | Inline prevention of API cyber-attacks targeting mission-critical applications without reliance on external infrastructure. |
| Testing | Assessment of APIs for conformance, risks, and sensitive data exposure before deployment. |

How Can A CNAPP Toolkit Helps?
In the chain of security, broken and undefended APIs are the weakest link. Developers hardly ever prioritize security over speed, features, usefulness, and user-friendliness. As a result, a series of exploitable vulnerabilities are created. Moreover, cloud-native APIs are frequently available online. If the proper security framework is not put in place, this may make them accessible to everybody. Because of this accessibility, hackers have an easier time breaking into cloud-based services and taking advantage of API flaws.
- The discovery engine’s runtime API Security monitors and filters system call activities of containerized workloads at runtime. Thus, preventing attacks on API endpoints. Our CNAPP solution also enforces least privilege principles and whitelists allowed system calls.
- Dynamic application security testing (DAST) on APIs to identify vulnerabilities. This is done by integrating with API gateways to analyze traffic between microservices.
- Continuously scan APIs to detect misconfigurations. It checks for compliance with the OWASP API Security Top 10.
- KubeArmor, an open-source discovery engine, monitors and filters incoming and outgoing network connections to APIs. This is useful when blacklisting or blocking unauthorized access or abuse. Aids you in enforcing network segmentation and zero trust.
- Runtime controls prevent the exploitation of unpatched vulnerabilities in API endpoints. KubeArmor can block attacks in real time before they reach the application layer.
- Our CNAPP security toolkit integrates Static application security testing (SAST), Software composition analysis (SCA), and API protection (DAST) results into one unified platform. Get full coverage and visibility into API vulnerabilities from code to runtime.
- Granular runtime controls on pod activities protect backend resources from abuse through APIs. Restrict pod access to only what is needed.
- A combo of Network traffic mirroring and eBPF means observability into API communications between microservices. Detecting anomalous behaviors has never been easier.
- Our CIEM provides identity and access management (IAM) for human and non-human identities accessing APIs.
- KubeArmor allows the creation of custom policies. These are useful when you wish to enforce security best practices for Kubernetes-hosted APIs. It recommends policies based on workload behaviors.

Conclusion
Although APIs are essential to contemporary cloud-native apps, attackers frequently target them. A multi-layered strategy is needed throughout the development lifecycle for comprehensive API security. The past year saw a 681% spike in API attacks.
The AccuKnox Enterprise CNAPP tool offers runtime controls, observability, and vulnerability management to safeguard APIs after deployment. Secure API design concepts, however, need to be incorporated from the beginning. OWASP offers great advice on best practices for API security. The security pillars of authentication, authorization, input validation, rate limitation, and encryption should be used by developers while designing APIs. To minimize API vulnerabilities before they can be exploited, a proactive security posture that combines secure SDLC and infrastructure protections should be implemented. This end-to-end security chain seamlessly incorporates the CNAPP tool.
All Advanced Attacks are Runtime Attacks
Zero Trust Security
Code to Cloud
AppSec + CloudSec

Prevent attacks before they happen
Schedule 1:1 Demo