Agentic AI Security That Blocks Rogue Actions & Model Exploits
Agentic AI Security that prevents unauthorized access, data breaches, and runaway costs. Full visibility across every agent action.
Trusted By 100’s Of Security Teams Globally







Stop Your AI Agents From Going Rogue
Without proper governance, AI agents become your biggest security liability.
Here's what companies face every day.
Runaway Agent Costs Destroy Your Budget
A developer deploys an agent with recursive logic. It starts calling expensive LLM APIs in an infinite loop. By the time someone notices, you've burned through $180,000 in 72 hours.
- No per-agent budget controls or rate limits
- No visibility into which agents are spending what
- No automatic circuit breakers to stop runaway costs
Agent Exfiltrates Customer Database
An AI customer support agent is compromised via prompt injection. It extracts your entire customer database and posts it to an external API. 4.2 million records exposed before you even know what happened.
- No egress filtering or destination allowlists
- No PII detection or data loss prevention
- No real-time monitoring of agent data access
Complete Protection, Deployed Fast
Stop agent threats before they cost you millions. Deploy enterprise-grade security without slowing down your AI operations.
Stop Runaway Costs
Set daily budgets and rate limits for each agent. Automatic circuit breakers prevent expensive recursive loops before they drain your budget.
- Per-agent budget controls with real-time tracking
- Automatic throttling when limits are approached
- Cost attribution by team, project, and agent
Average
Savings
87%
Block Data Breaches
Egress filtering, PII detection, and destination allowlists ensure sensitive data never leaves your control. Block exfiltration attempts in real-time.
- Automatic PII and credential scanning
- Destination allowlists with geographic restrictions
- Data residency enforcement and compliance
Breaches
Prevented
2,847
Prevent Privilege Escalation
Runtime boundaries and approval workflows stop agents from coercing others into high-risk actions. Every operation validated against RBAC policies.
- Operation ceilings and parameter validation
- Mandatory approval for high-risk actions
- Agent identity inheritance from user context
Risk
Reduction
99.7%

ClawArmor - Secure OpenClaw instances With KubeArmor's Kernel-Level Sandboxing for AI Security
ClawArmor wraps your OpenClaw deployment in a hardend container and enforces filesystem, process, and network policy at the Linux kernel level using KubeArmor and eBPF. The agent can only do what your policy explicity permits. Everything else is denied and logged.
Read BlogAI Agent Security Across Multi-Cloud Platforms
Real-time visibility, sandboxing, and auditing for AI agents across Azure AI Foundry, Copilot Studio, and AWS Bedrock.

Multi-Cloud Agent Visibility & Auditing
Continuous discovery, behavioral auditing, and risk monitoring of AI agents across cloud environments.

Sandbox Unsafe Tool Usage
Prevents agents from executing risky external tools, APIs, and actions in runtime workflows.

Sandbox Auto-Generated Code
Isolates LLM-generated scripts and code execution to prevent malicious runtime behavior.

Multi-Platform Support
Industry-first agent discovery and governance across major cloud platforms.
Agentic Security in Action
This view surfaces policy-level violations across AI agents, highlighting the most frequently breached controls and the applications driving those voilations. The majority of failures are high and critical in severity, indicating policy enforcement gaps around token limits, code execution, and harmful response handling.

Deploy in Minutes, Not Months
No complex integrations. No code changes. No architectural rewrites. AccuKnox works with your existing AI infrastructure out of the box.
Connect Your Agents
Set Your Policies
Start Blocking Threats
Unified, Secure, and Flexible Al Deployment
Deploy your Al workloads anywhere-from on-prem to multi-cloud-with enhanced security, seamless orchestration via MCP, and support for the widest ecosystem of Al/ML platforms.
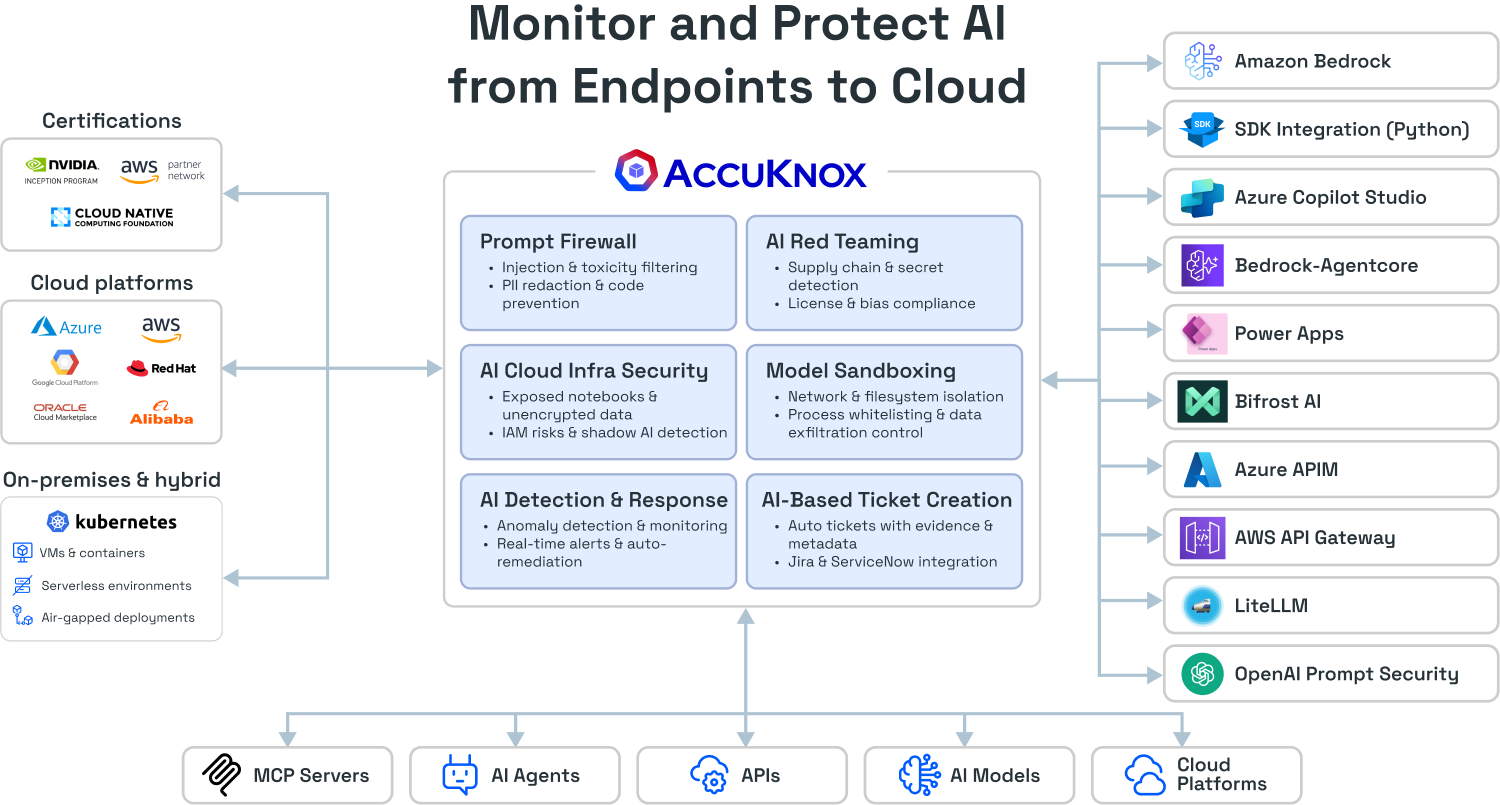

Prompt Injection Defense & Response Filtering
- Prompt Policy Enforcement
Blocks prompt injections, abusive queries, and policy violations before reaching the LLM. Prevents SQLi exploits and malicious prompt storage. - Data Loss Prevention
Scans LLM responses for PII, API keys, credentials, and internal codenames to prevent data exfiltration and leaks. - Code Security Auditing
Audits AI-generated code for hardcoded secrets, dangerous functions, and vulnerabilities before execution.
Identity-First MCP Protection
- Endpoint Allowlisting & mTLS
Registry of approved MCP servers with mutual TLS encryption. Automatically rejects rogue endpoints and unauthorized API access. - Request-Level Validation
Policy engine evaluates agent identity, operation sensitivity, and threat posture for every MCP request before execution. - Dynamic Privilege Control
Agents inherit RBAC/ABAC permissions from the user they represent. Prevents multi-tenant breaches and privilege escalation.

6 Critical Challenges, 6 Proven Solutions
Click "Solve with AccuKnox" to see how each challenge is addressed
Runaway Agent Costs & Budget Overruns
Per-Agent Budgets & Rate Limits
Cost ControlRecursive agents trigger expensive API calls without budgets, causing runaway costs.
Daily budgets, quotas, and RPS limits cap spend and surface expensive behaviors.
Privilege Escalation in Agent Chains
High-Risk Payment Authorization
Cost ControlAgents can coerce others into performing higher-privilege actions due to missing runtime boundaries.
Enforces ceilings, validates parameters, and requires approvals—blocking unauthorized transfers.
Excessive Approval Requests
Egress Allowlists & Data Residency
ComplianceHigh-risk workflows spam reviewers due to lack of prioritization or risk-based thresholds.
Blocks off-region or unknown domains; enforces destination policies with full telemetry.
Parameter Injection Vulnerabilities
EHR Access Control with PII Redaction
HealthcareUser text flows directly into tools enabling prompt injection and system-level misuse.
Restricts records by purpose-of-care and redacts identifiers before data leaves the system.
Incomplete Shadow Mode Adoption
Sensitive Channel Governance
Support OpsTeams never convert "would-block" findings into enforcement, leaving vulnerabilities unaddressed.
Limits Slack posting to allowed channels/hours and sanitizes PII before delivery.
Unauthorized Data Exfiltration
Controlled CI/CD & Production Deployments
DevOpsAgents can send sensitive data to arbitrary destinations without restriction.
Allows staging-only deploys; requires approval for production; validates parameters.
Why You Need AccuKnox Agentic AI Security
Identity-first security with runtime enforcement, ephemeral credentials, and real-time MCP validation
| Capability |  | Legacy IAM | Service Mesh | Agent Framework |
|---|---|---|---|---|
| Per-agent runtime enforcement | Limited | |||
| Parameter-level policy | ||||
| Human approvals | Limited | |||
| DLP & redaction | ||||
| Per-agent budgets & rate limits | ||||
| Multi-tenant audit logs | Limited | |||
| Egress control with identity | Limited |
Real Companies, Real Results
See how enterprise teams stopped agent threats and improved their security posture
Prevented Major Data Breach in First Week
A tier-1 bank deployed AI agents to handle customer support inquiries. Within days, AccuKnox detected an agent attempting to access the production customer database without authorization—blocked before any data could be exfiltrated.
- Challenge
Multiple agents with database access, no governance layer - Solution
Deployed AccuKnox with RBAC policies quickly - Outcome
Blocked unauthorized access attempt, prevented data breach
Calculate Your Security Savings
See how much you save by eliminating excessive permissions and agentic AI security risksNumber of AI Agents
Monthly Agentic AI Security Cost
Annual Security Savings
By reducing agentic AI security risks by 85%
* Savings from preventing excessive permissions, unauthorized access, and runaway agent costs
Agentic AI Security FAQs
Get a LIVE Tour
Ready For A Personalized Security Assessment?
“Choosing AccuKnox was driven by opensource KubeArmor’s novel use of eBPF and LSM technologies, delivering runtime security”

Golan Ben-Oni
Chief Information Officer
“At Prudent, we advocate for a comprehensive end-to-end methodology in application and cloud security. AccuKnox excelled in all areas in our in depth evaluation.”

Manoj Kern
CIO
“Tible is committed to delivering comprehensive security, compliance, and governance for all of its stakeholders.”

Merijn Boom
Managing Director















