Defend Against Shadow AI and Prompt Attacks with AI-SPM Red Teaming
Address modern AI Threats Zero Trust prompt and Sandboxing
Common AI Compliance & Security Challenges
Compliance Challenges
Adhering to industry and regulatory standards is quite complex.
Lack of Visibility
Organizations struggle with monitoring AI/ML pipelines for security risks.
Misconfigurations
Applications, Models, Workloads and environment often lack proper security controls.
AI Model Vulnerabilities
AI models face threats like adversarial attacks, data poisoning, and unauthorized access.
Data Security Risks
Sensitive data can be exposed during AI model training and inference.
Is Your AI Risk Free & Compliant ?
Check Our Solution
Use Cases of our AI Security Platform
-
AI Governance, Risk, and Compliance (AI-GRC)
- Supports NIST AI, MITRE AI, AISCP, SOC, and more.
- Automates audit trails and policy checks.
- Enhances visibility and control over AI governance.
-
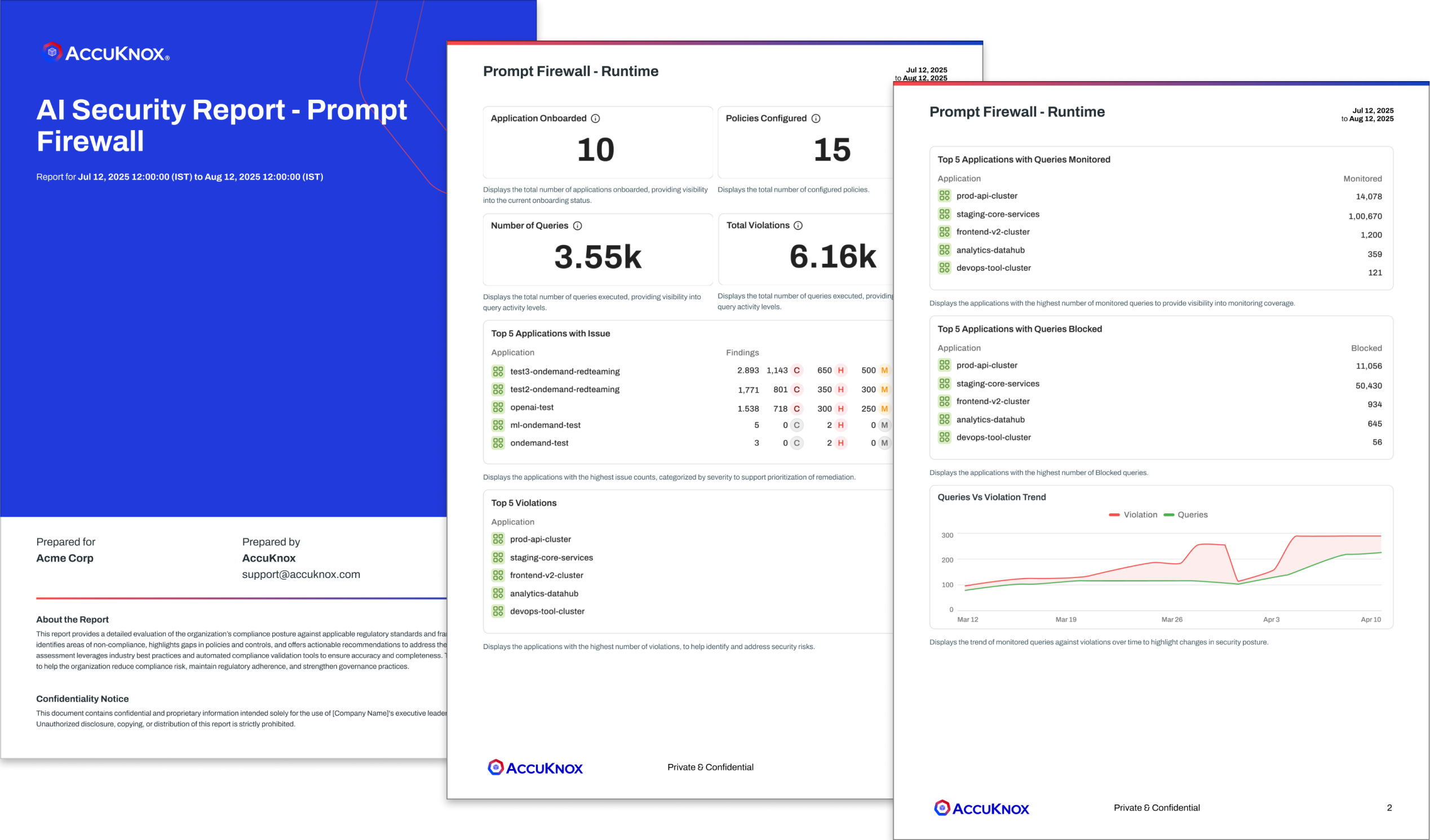
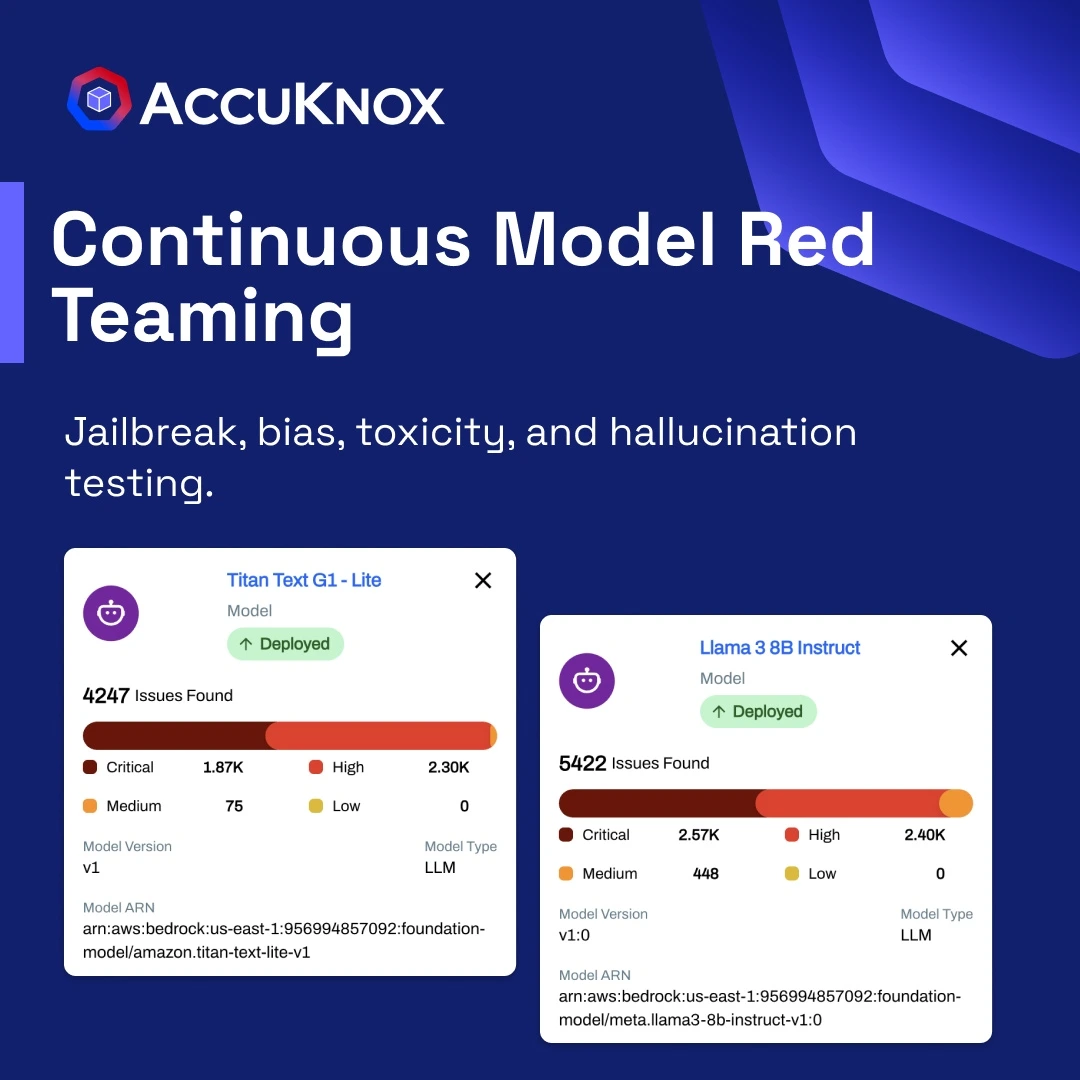
Automated Red Teaming
- Dynamically tests AI models for vulnerabilities.
- Automated adversarial attack simulation to proactively identify weaknesses.
-
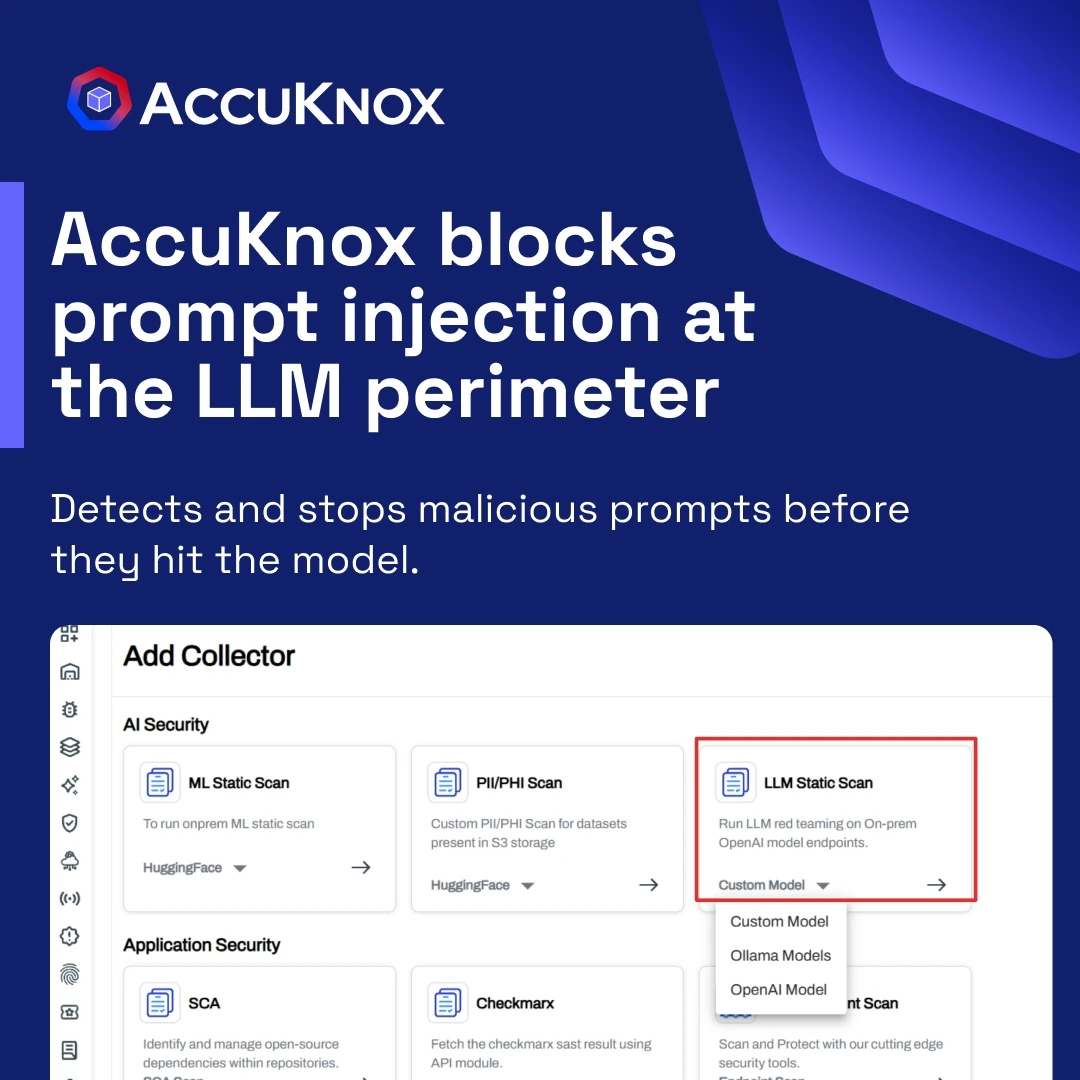
LLM Prompt Firewall
- Protects against prompt injection attacks.
- Ensure safe and controlled interactions in LLM-based applications.
-
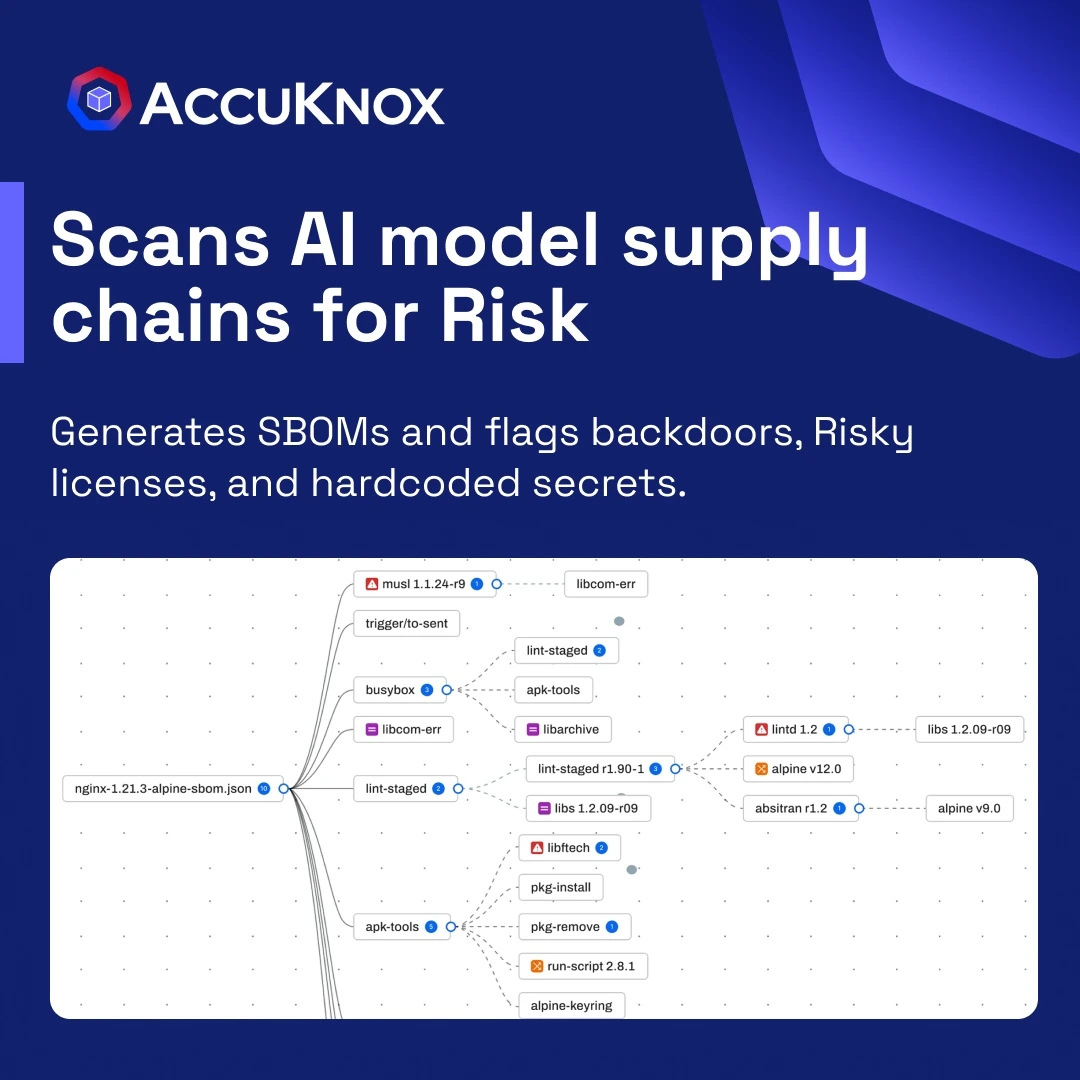
Training Pipeline Security
- Secures model training pipelines and artifacts.
- Safeguards trained AI models from theft, tampering, or malicious alterations.
-
Data Security
- Detecting PII/PHI exposure.
- Prevents dataset tampering.
- Prevents unauthorized access.


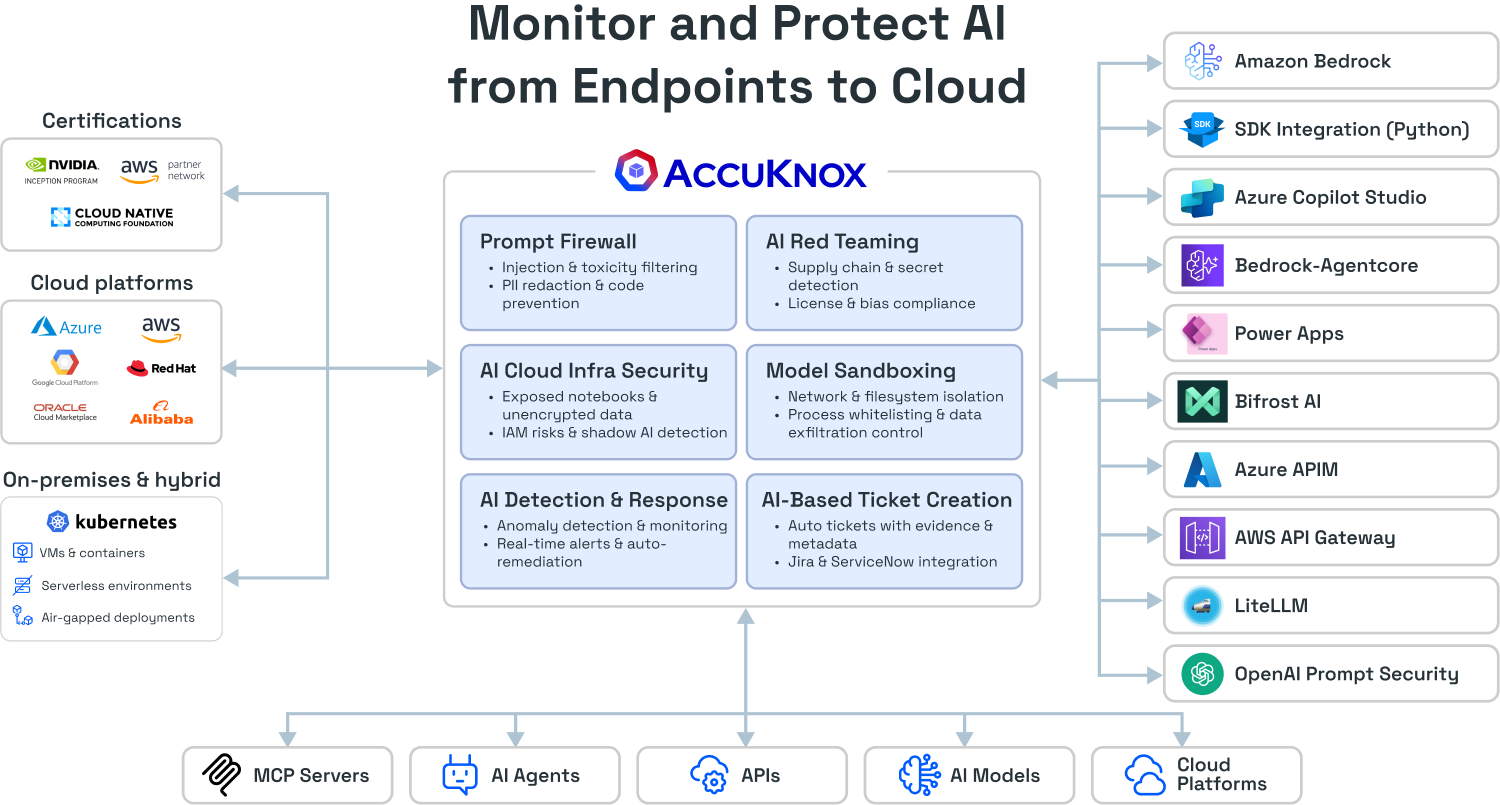


Get Scheduled & On-Demand Reports for AI Security
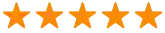
AI Security Modules
AI Security Posture Management (AISPM)
AI Deployment Security
AI Data Security
AI Runtime Security
AI Red Teaming
AI Governance & Compliance
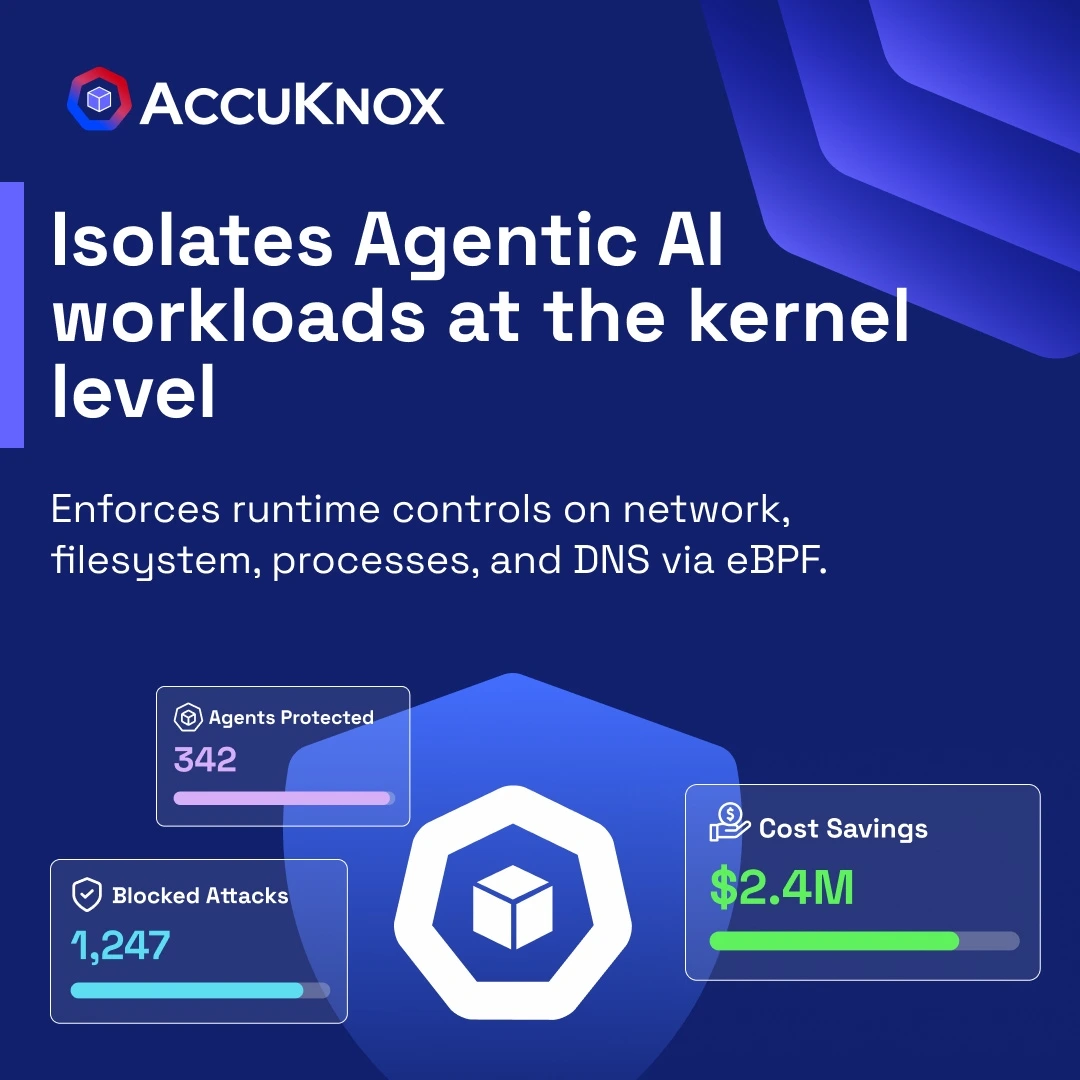
AI Agent Security Across Multi-Cloud Platforms
Real-time visibility, sandboxing, and auditing for AI agents across Azure AI Foundry, Copilot Studio, and AWS Bedrock.

Multi-Cloud Agent Visibility & Auditing
Continuous discovery, behavioral auditing, and risk monitoring of AI agents across cloud environments.

Sandbox Unsafe Tool Usage
Prevents agents from executing risky external tools, APIs, and actions in runtime workflows.

Sandbox Auto-Generated Code
Isolates LLM-generated scripts and code execution to prevent malicious runtime behavior.

Multi-Platform Support
Industry-first agent discovery and governance across major cloud platforms.
AI Model Cards for Continuous Governance
Transform your model documentation from static reports into a real-time security and risk dashboard.
- Continuous Security & Supply Chain
Get a live Software Bill of Materials (SBOM), real-time vulnerability scanning, and ongoing license compliance checks for all model components. - Automated Validation & Risk Scoring
Use sandbox-driven assessments for automated red teaming, evaluating safety, bias, toxicity, jailbreak resilience, and assigning a dynamically changing risk score. - Runtime Observability & Fencing
Establish behavior baselines and monitor operational activity to detect policy violations and ensure real-time data isolation and fencing of model data stores.

AI Security Use Cases
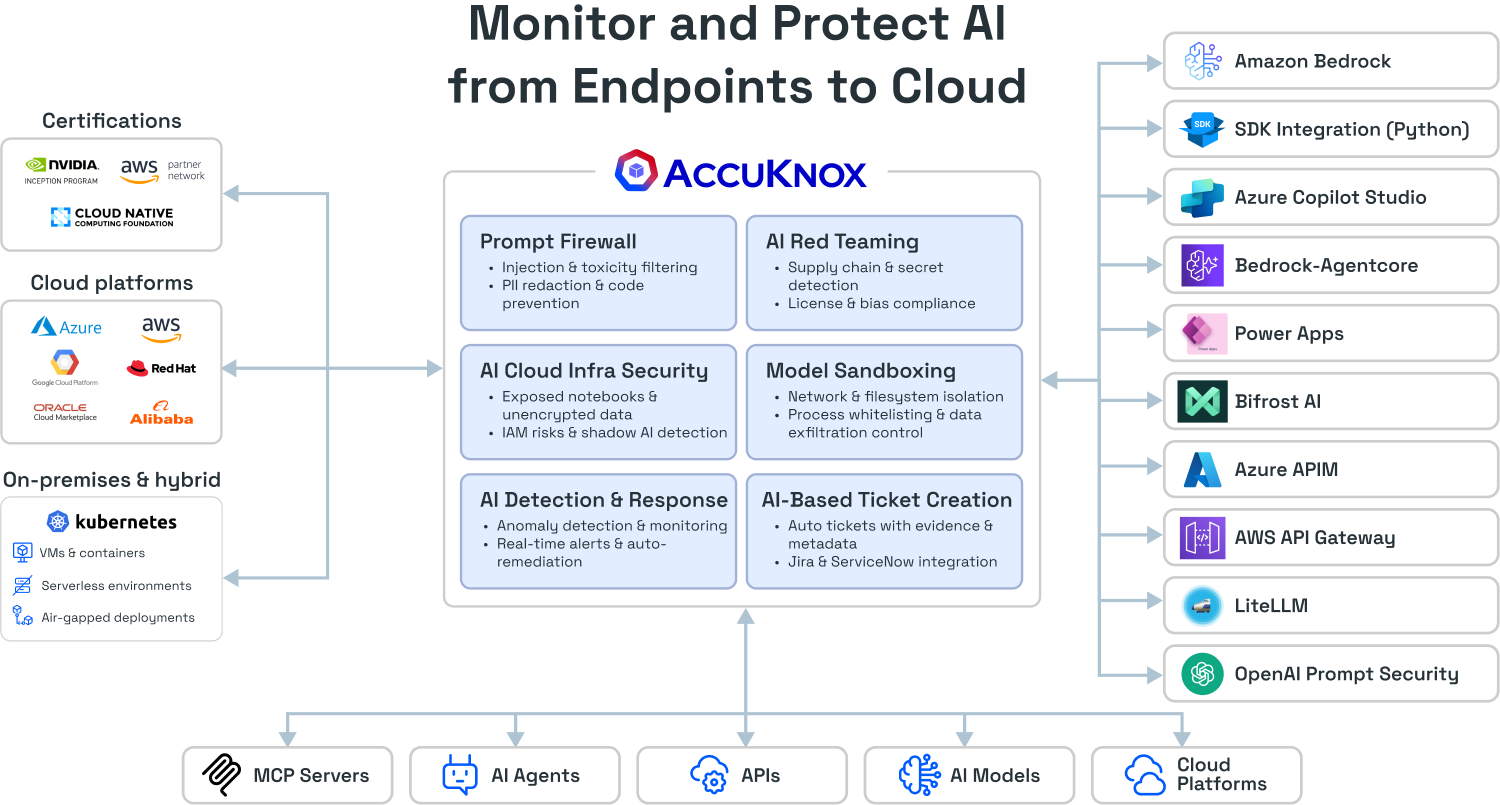
Prompt Firewall
- Prompt Injection Defense
- PII & Secrets Redaction
- Toxicity Filtering
- Code Execution Prevention
AI Red Teaming
- Supply Chain Security (Malicious payloads)
- Prompt Leakage Risk (Hardcoded secrets)
- License Compliance (Restrictive licenses)
- Bias & Toxicity Detection
AI Cloud Infra Security
- Exposed Notebooks (Public access)
- Unencrypted Training Data
- Over-Permissive Roles (IAM risks)
- Shadow Al Assets (Unapproved instances)
Model Sandboxing
- Agentic Network Isolation (API restrictions)
- File System Protection (Read-only paths)
- Process Whitelisting (Block sub-shells)
- Data Exfiltration Control (DNS filtering)
AI Detection & Response
- Al activity monitoring across cloud and models
- Policy-based anomaly detection
- Real-time alerts and automated remediation
- Full audit trail of Al actions
AI-Based Ticket Creation
- Automatic ticket creation from Al security alerts
- Context-rich tickets with evidence and metadata
- Integration with Jira and ServiceNow
- Workflow-driven remediation tracking
AccuKnox AI-SPM Delivers Security At Every Layer of AI






Talk to Security Experts

Ready to Protect Your Sensitive Cloud Assets?
Unified, Secure, and Flexible Al Deployment
Deploy your Al workloads anywhere-from on-prem to multi-cloud-with enhanced security, seamless orchestration via MCP, and support for the widest ecosystem of Al/ML platforms.
AI Security Key Differentiators
Runtime prompt firewall with LLM-as-judge sanitization and blocking
Automated AI red teaming for injections, hallucinations, toxicity, bias
Multi-layer AI security across models, agents, datasets, and pipelines
AI asset inventory with agent, model, and pipeline lineage mapping
AI detection and response for model misuse and infra misconfigurations

Detect and block AI-specific threats via model red-teaming, prompt filtering, dataset integrity checks, and secure ML supply-chain controls.
AI Security Competitive Stack Ranking

AI Security for AI/LLM Workload Security FAQs
Get a LIVE Tour
Ready For A Personalized Security Assessment?
“Choosing AccuKnox was driven by opensource KubeArmor’s novel use of eBPF and LSM technologies, delivering runtime security”

Golan Ben-Oni
Chief Information Officer
“At Prudent, we advocate for a comprehensive end-to-end methodology in application and cloud security. AccuKnox excelled in all areas in our in depth evaluation.”

Manoj Kern
CIO
“Tible is committed to delivering comprehensive security, compliance, and governance for all of its stakeholders.”

Merijn Boom
Managing Director
Trusted by Cybersecurity Leading Investors
Featured Customers







Awards & Recognitions








Investors








About Us
AccuKnox delivers a Zero Trust Security platform for AI, API, Application, Cloud, and Supply Chain Security. Incubated out of R&D innovator, SRI International (Stanford Research Institute), AccuKnox holds seminal Zero Trust security patents and is backed by top-tier investors including National Grid Partners, Dolby Family Ventures, Dreamit Ventures, Avanta Ventures, and the 5G Open Innovation Lab.