
Full API Visibility: A Practical Guide to API Security Platforms That Show You Everything (2026)
The core problem You can’t secure what you can’t see. Most enterprises discover they have 40-60% more APIs than their gateway configurations show — shadow APIs, zombie endpoints, and untracked microservice connections that leave critical business logic exposed. The API Visibility Gap: Root Cause Analysis Most security teams know they have a visibility problem. Fewer […]
Reading Time: 5 minutes
TL;DR — 5 Key Takeaways
- Gateways only see traffic routed through them. 40–60% of APIs microservice calls, pod-to-pod traffic, AI connections; never touch a gateway.
- Gateway Blind Spots, Sampling Gaps, Agent Gaps, Drift Gaps, and LLM API Connection Gaps each have distinct root causes and require different fixes.
- Gateway inspection, code scanning, and sampled traffic analysis combined still leave Sampling Gaps and Agent Gaps structurally open.
- eBPF operates at the kernel level with zero sampling, capturing 100% of API calls across all languages, frameworks, and traffic directions without code changes.
- Score any platform on kernel observability, zero sampling, east-west coverage, drift detection, and LLM mapping before you commit to a purchase.
The core problem
You can’t secure what you can’t see. Most enterprises discover they have 40-60% more APIs than their gateway configurations show — shadow APIs, zombie endpoints, and untracked microservice connections that leave critical business logic exposed.
The API Visibility Gap: Root Cause Analysis
Most security teams know they have a visibility problem. Fewer understand why it exists structurally — and that gap in understanding is why most evaluations end up solving symptoms rather than causes.

Why gateways cannot see everything
Gateways only see traffic explicitly routed through them — internal microservice calls, pod-to-pod traffic, and Kubernetes sidecar communication never touch a gateway. This isn’t a configuration problem. Microservices, Kubernetes ephemerality, and AI-generated runtime connections each compound the gap structurally. They are architectural inevitabilities.
The three architectural shifts that created the gap
1. The microservices explosion. A monolithic application might expose a handful of external API endpoints. The equivalent microservices architecture exposes hundreds of internal service-to-service endpoints — most communicating via direct HTTP/gRPC calls that never touch an API gateway. Every microservice boundary is a potential blind spot.
2. The Kubernetes dynamic. Kubernetes environments are intentionally ephemeral. Pods spin up and down continuously in response to load. Static inventory methods — gateway registrations or agent deployments — cannot keep pace. A pod that existed for 20 minutes may have handled thousands of API calls now invisible in any permanent inventory.
3. The AI API layer. The newest dimension of the gap. AI-powered applications generate API calls at inference time — calls to model endpoints, vector databases, tool-use APIs, and MCP servers determined by runtime context, not any static specification. These connections are architecturally invisible to every discovery method that operates at the code or gateway layer.
The Five Named API Visibility Gap Types
The industry talks about ‘blind spots’ generically. This guide names them precisely — because named, defined concepts are the prerequisite for systematic solutions. Each gap type has a distinct root cause and requires a different remediation approach.
| 1 | Gateway Blind Spots [Largest category] APIs that receive traffic but were never registered with any gateway. Includes microservice-to-microservice calls, internal platform APIs, and debug endpoints deployed outside CI/CD. Gateways enforce policy on managed APIs — they cannot structurally discover unmanaged ones. |
| 2 | Sampling Gaps | Probabilistic risk Traffic analysis tools capture only 1–10% of API calls. A 5% sample means 95% of calls are unobserved. Low-frequency, high-value calls — admin endpoints, privilege escalation paths — run within the unsampled window. An attacker making one call every ten minutes has a 90% chance of going undetected against a 10%-sampling tool. |
| 3 | Agent Gaps | Kubernetes risk Agent-based tools require installation on each host or pod. In dynamic Kubernetes environments, pods spin up faster than agents deploy. The window between pod creation and agent installation is a live blind spot — an architectural incompatibility between point-in-time installation and continuously ephemeral infrastructure. |
| 4 | CI/CD-Only Gaps (Drift Gaps) | Runtime divergence Code scanning produces an accurate inventory at deployment — and nothing after. APIs change at runtime: parameters added, endpoints modified, authentication requirements shifted. PCI DSS v4.0.1 requires the API security perimeter to reflect the actual runtime surface — structurally unsatisfiable by any purely static approach. |
| 5 | LLM API Connection Gaps | 2026 frontier AI applications generate API calls at inference time — to vector databases, model endpoints, MCP servers — not declared in any static spec. These connections are ephemeral and invisible to any discovery method operating at the code or gateway layer. The fastest-growing category of undocumented API traffic in 2026. |
The 4-Method API Discovery Comparison Framework
Four distinct technical approaches to API discovery exist. Most platforms use one or two. True full visibility requires understanding what each covers — and where each structurally fails.
| Discovery Method | What It Sees | Structural Blind Spots | Gap Types Addressed |
|---|---|---|---|
| Gateway Inspection | Managed external APIs on registered routes. North-south traffic through the gateway. | East-west internal traffic. Unregistered APIs. Dynamic endpoints. Pod-to-pod calls. | Creates Gateway Blind Spots. Does not independently address any gap type. |
| Code / Spec Scanning | APIs declared in specs or code at deployment. Framework-detected routes. | Runtime drift. Dynamic routes. APIs outside CI/CD. LLM connections. Any post-deployment change. | Baseline inventory only. Creates Drift Gaps. Cannot address Sampling, Agent, or LLM Gaps. |
| Traffic Analysis (Sampled) | Active APIs with high-frequency traffic during the observation window. | Low-frequency calls. Admin endpoints. Traffic outside the sampling window. | Partially addresses Gateway Blind Spots. Creates Sampling Gaps. Cannot address Agent or LLM Gaps. |
| eBPF Runtime Discovery | 100% of API calls — internal and external. East-west traffic. Dynamic endpoints. LLM connections. Zombie and shadow APIs across all namespaces. | Requires Linux kernel. No historical data before sensor deployment. | Addresses all five gap types simultaneously. The only method that closes every gap type. |
Combining all three still leaves Sampling Gaps and Agent Gaps structurally open. eBPF operates at a fundamentally different layer — the kernel — and eliminates the structural constraints that limit all other approaches.
The API Visibility Coverage Assessment Framework
Use this five-point framework to score any API security platform before purchase. Each point is binary: the platform satisfies it completely, or it does not. A platform scoring 3/5 has structural blind spots — not feature gaps.
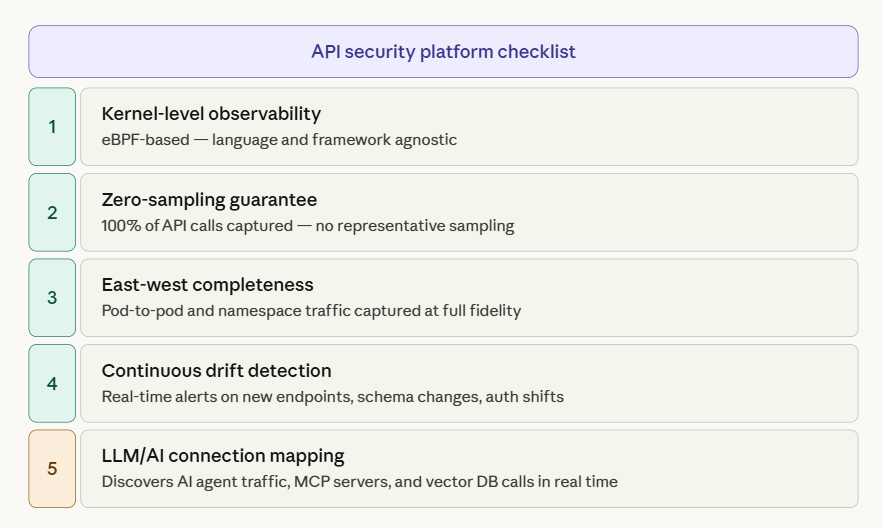
| 1 | Kernel-level observability Does the platform observe API traffic at the OS/kernel level, independent of application code, language, or framework? Requires eBPF or equivalent. SDK injection and network-layer taps cannot satisfy this point. Why it matters: Kernel-level observation is the only method universal across heterogeneous environments. The kernel sees Python, Go, Java, and Node.js equally — without instrumentation. |
| 2 | Zero-sampling guarantee Does the platform guarantee 100% of API calls are captured? Look for explicit language about sampling rates in technical documentation. Any use of ‘representative traffic’ in vendor copy describes a sampling approach. Why it matters: Attackers use low-frequency call patterns to avoid anomaly detection. A 10% sampling rate gives an attacker making one call every 10 minutes a 90% chance of going undetected per observation window. |
| 3 | East-west completeness Does the platform capture API calls between internal services — pod-to-pod, namespace-to-namespace, sidecar-to-sidecar — with the same fidelity as external traffic? Test this in any proof-of-concept. Why it matters: Lateral movement in cloud-native environments exploits east-west API paths. If visibility stops at the gateway, threat detection stops there too. |
| 4 | Continuous drift detection Does the platform continuously compare the runtime API surface against its baseline — detecting new endpoints, modified schemas, changed authentication — and alert in real time? Why it matters: PCI DSS v4.0.1 requires the API security perimeter to reflect the actual runtime surface. An endpoint added post-deployment is simultaneously outside your security controls and your compliance documentation. |
| 5 | LLM/AI connection mapping Does the platform discover and inventory API calls made by AI agents, LLM pipelines, and tool-use frameworks — including calls to model endpoints, vector databases, and MCP servers — in real time? Why it matters: AI-generated API connections are the fastest-growing category of undocumented traffic in 2026. Without this, enterprises cannot enforce least-privilege access for AI workloads or detect compromised agents. |
How AccuKnox Achieves Full API Visibility
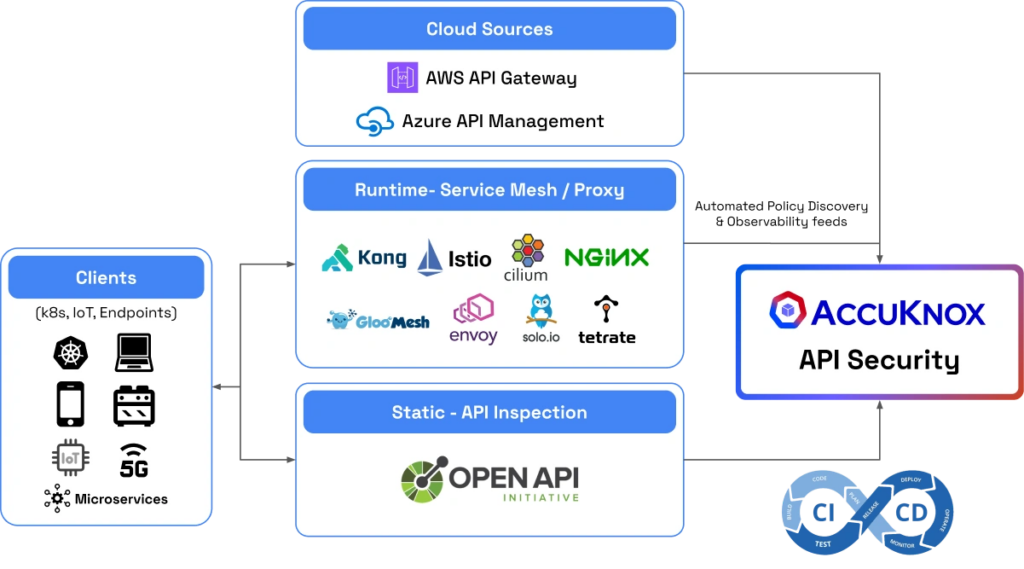
Runtime API Security
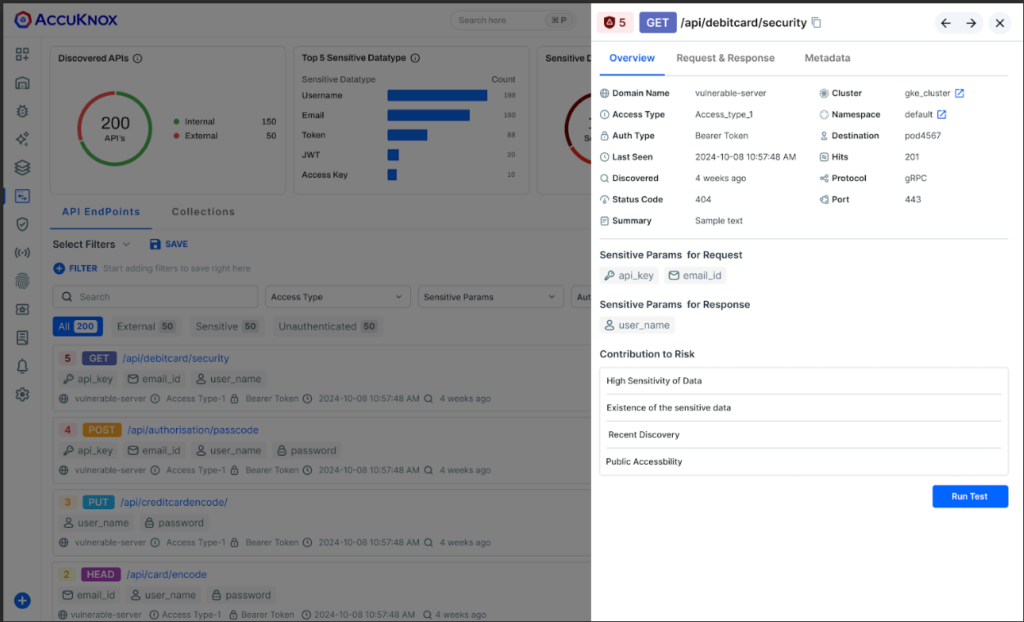
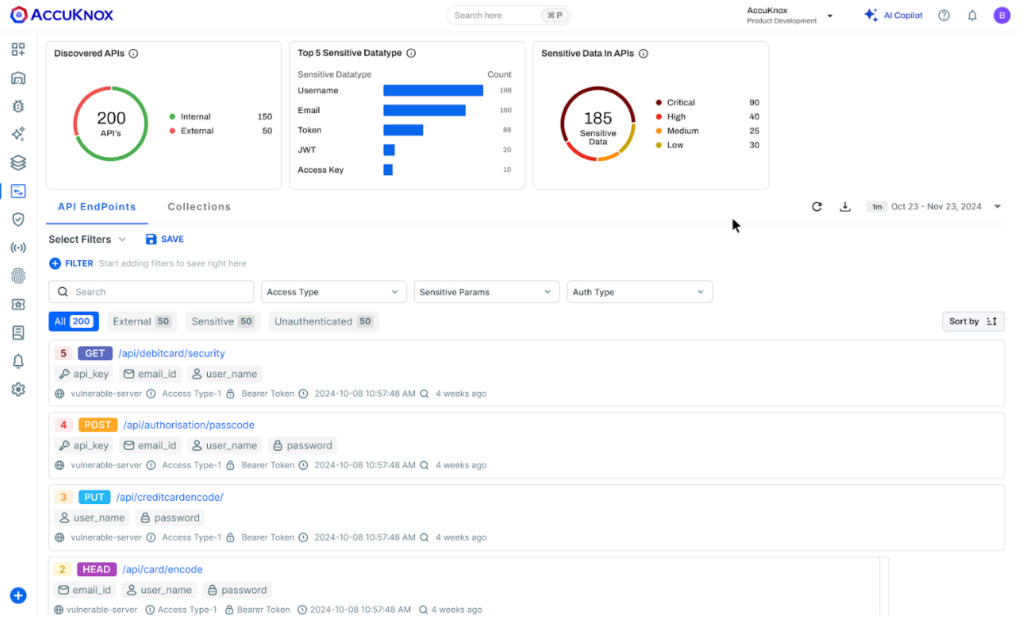
- Uses service mesh sidecars or proxies to inspect secure traffic and detect anomalies.
- Exports API instrumentation data in OpenTelemetry format for seamless monitoring.
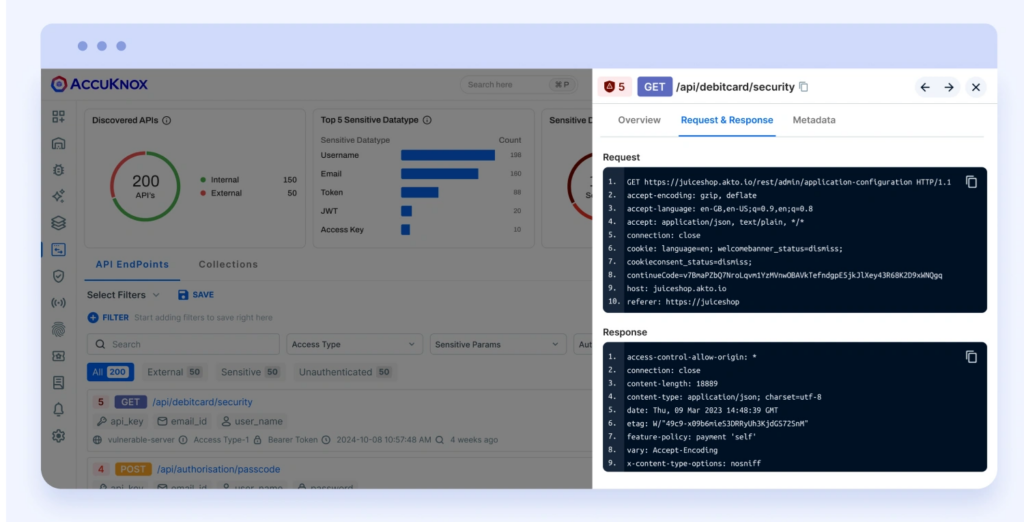
- Identifies access patterns with a discovery engine and provides a SaaS or on-prem control plane for management.
- Identifying sensitive data assets in API headers, responses
Static API Security
- Scans code repositories and analyzes API specs (OpenAPI, Swagger, WSDL) for security gaps.
- Extracts endpoint details, peer connections, and access requirements for better enforcement.
- Integrates into CI/CD pipelines to detect and mitigate risks before deployment.
API Security Testing
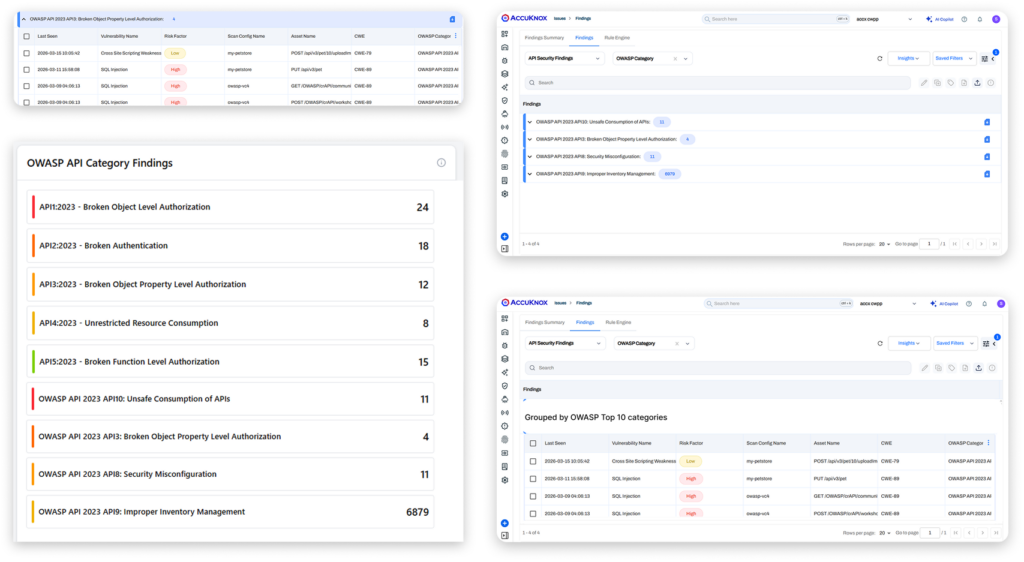
- Identify vulnerabilities including OWASP Top 10 for API.
- Detects and mitigates injection attacks, broken authentication, and other critical threats.
- Identifying Shadow, Zombie, and Orphan APIs
LLM API connection discovery
Outbound connections from AI workloads are captured at the kernel network layer regardless of LLM framework or orchestration system. Every call to a model serving API, vector database, or MCP server is surfaced with full workload identity context — which pod, service account, and namespace initiated it. This provides ground-truth AI API inventory that static analysis cannot deliver, because the specific endpoints called are determined by runtime inference decisions, not by any static specification.
Running a Visibility Gap Assessment
| 1 | Establish the gateway inventory baseline Export all registered APIs from every gateway in your environment — Kong, AWS API Gateway, NGINX, Istio, or any other active gateway. This is your starting count and your denominator for the gap calculation. |
| 2 | Deploy eBPF runtime discovery for 72 hours Run in parallel across a representative production subset covering both internal microservices traffic and externally visible APIs. 72 hours captures enough traffic variability to surface low-frequency endpoints. |
| 3 | Calculate your gap Divide runtime-discovered APIs by gateway count. 1.4× = 40% gap. 1.6× = 60% gap. This is your organisation’s actual number — not an industry benchmark. |
| 4 | Classify and score Categorise delta APIs by gap type using the five named types from Section 02. Then apply the five-point framework to your current tooling. A score below 4 indicates structural limitations that configuration changes cannot fix — only a platform with different architectural foundations can close them. |

API Security 1 Pager
Read the Full Guide on API Security
Explore AccuKnox API Security Platform
Schedule a Free Demo
API Visibility Is the Foundation, API Security is the Endgame
The visibility problem is solvable — but requires architectural honesty. Gateways are management tools, not discovery tools. Code scanning is shift-left, not runtime truth. Sampled analysis is probabilistic, not deterministic. None of these methods, individually or in combination, satisfies the five dimensions of full API visibility.
eBPF-based continuous runtime discovery — kernel-level, zero sampling, across all traffic paths and protocols — is the direct technical answer to the structural visibility problem every enterprise running APIs at scale faces in 2026.
Frequently Asked Questions
What is full API visibility?
Every API endpoint — internal, external, documented, undocumented — known to your platform in real time, with zero sampling and continuous drift detection. Gateways, static scanning, and sampled traffic alone cannot achieve it.
What are shadow APIs?
Endpoints receiving live traffic that were never registered or documented. They evade gateway and spec-based discovery by definition — eBPF catches them at the kernel level regardless of whether they exist in any spec.
How do I discover zombie APIs?
Compare your API spec against runtime traffic. Any deprecated endpoint still receiving calls is a zombie. Requires 100% traffic capture — sampled tools miss zombie APIs because they call infrequently.
What is the difference between gateway discovery and eBPF discovery?
Gateways see only registered routes. eBPF sees every network connection at the kernel level — registered or not, internal or external. The gap between their inventories is your visibility gap.
Get a LIVE Tour
Ready For A Personalized Security Assessment?
“Choosing AccuKnox was driven by opensource KubeArmor’s novel use of eBPF and LSM technologies, delivering runtime security”

Golan Ben-Oni
Chief Information Officer
“At Prudent, we advocate for a comprehensive end-to-end methodology in application and cloud security. AccuKnox excelled in all areas in our in depth evaluation.”

Manoj Kern
CIO
“Tible is committed to delivering comprehensive security, compliance, and governance for all of its stakeholders.”

Merijn Boom
Managing Director



















