
API Security That Goes Deeper – How AccuKnox Discovers, Classifies, and Secures Every Endpoint
Most API security tools watch the front door. AccuKnox watches everything — external traffic, internal microservice calls, undocumented endpoints developers forgot existed, and deprecated APIs that never got turned off. Here’s a full breakdown of what the platform actually does.
Reading Time: 7 minutes
TL;DR
- AccuKnox closes the L7 visibility gap by adding API observability alongside file, process, and network layers.
- Auto-discovers endpoints by connecting to existing gateways (AWS API Gateway, Istio, Kong, NGINX) — no code changes needed.
- Live traffic is scanned for PII, PHI, and credit card data, filterable by sensitivity, auth type, and status code.
- Uploading a Swagger/OpenAPI spec instantly classifies endpoints as Shadow, Zombie, or Orphan.
- Pricing is based on unique endpoint count — not traffic volume — so costs stay predictable.
How AccuKnox Discovers, Classifies, and Secures Every Endpoint
Most security tools claim “full visibility.” Few can actually back that up across every layer of your stack. AccuKnox API Security was built to close the one gap that was genuinely missing — the API layer — and connect it to everything else the platform already sees.
Here’s what that actually means in practice.

The Missing Layer
AccuKnox already had visibility into:
- Network layer (L3/L4) — via KubeArmor-based network segmentation
- Process execution — what’s running inside your workloads, with process whitelisting
- File system access — syscall-level visibility into file paths being accessed
What was missing was L7 / API-level visibility. Without it, achieving a true Zero Trust security posture is impossible. You couldn’t answer critical questions like: “How many of my services are calling OpenAI APIs?”—a vital query for discovering and governing AI agents. That is exactly the challenge our API security platform solves.

AccuKnox provides a unified 360° view across file, process, network, and API layers — all in a single platform.
Part 1: API Discovery & Inventory
The first job of the feature is to find all your APIs — automatically — across your entire environment.
What Gets Discovered
Once connected to your environment, AccuKnox surfaces:
- All API endpoints — with method, path, host, status codes, and hit counts
- Sensitive parameters — PII (names, emails), PHI (health data), credit card numbers, private IPs detected in request/response bodies and headers
- Authentication posture — which APIs use bearer tokens or other auth, and which are completely unauthenticated
- Secure vs. insecure connections — HTTP vs. HTTPS across your traffic
- North-south AND east-west traffic — most vendors only look at external traffic. Up to 80–90% of real-world traffic is internal microservice-to-microservice communication. AccuKnox covers both.

API Endpoints list filtered by Sensitive Params, showing /cart/checkout tagged with pii-us-credit-card and information about running server. PII and PHI are automatically detected in live request/response traffic — no manual tagging required.

Every endpoint carries rich metadata: hit count, last seen, cluster, protocol, port, and exactly which sensitive data was observed.
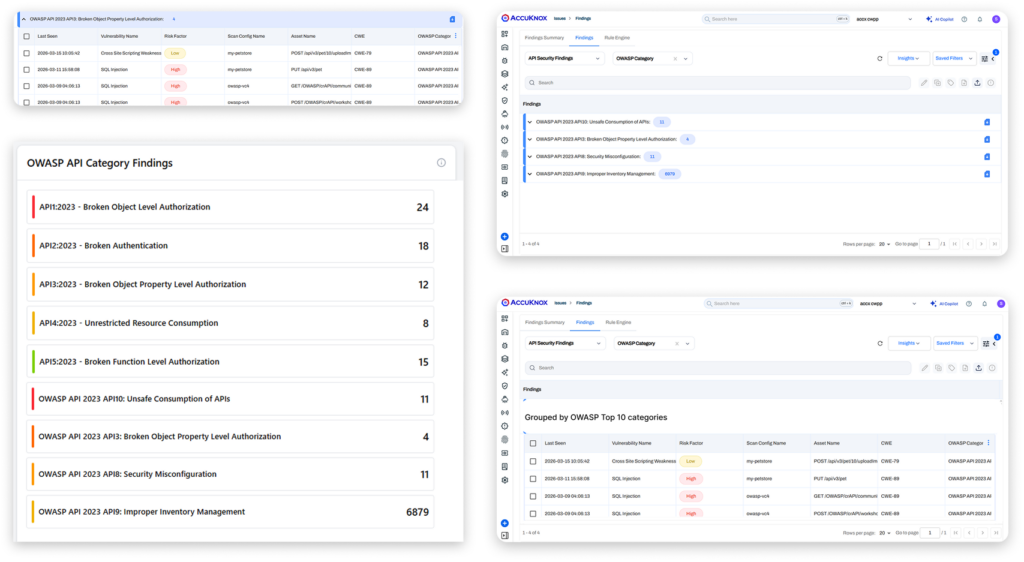
AccuKnox Provides Visibility on OWASP Top 10 Findings for API Security
How It Connects to Your Environment
AccuKnox doesn’t require you to instrument your code. It hooks into the connectors and gateways you already use:
- Cloud-managed: AWS API Gateway, Azure APIM, F5 BIG-IP
- On-prem / Kubernetes: Istio Gateway, Ingress NGINX (including F5 NGINX), Kong, MuleSoft, Envoy (native support — covers Gloo Mesh, Tetrate, Solo, and more)
You connect one or more of these, and API endpoints start populating automatically. Most organizations use multiple connectors — AccuKnox aggregates them all into a unified inventory.

AccuKnox connects to your existing gateways and proxies — cloud, on-prem, and Kubernetes — with no code changes required.
Collections: Auto-Organized by Microservice
APIs are automatically grouped into collections based on hostname, path patterns, or HTTP method — one collection per microservice. This gives you a structured view of your environment from day one, not a flat list of thousands of endpoints.
You can also create custom collections using hostname regex, path regex, or method filters.

Collections automatically organize endpoints by microservice. Custom rules let you group by hostname, path pattern, or HTTP method.
Part 2: Shadow, Zombie & Orphan APIs
This is where things get genuinely useful. Once you have an inventory, AccuKnox compares it against your API specification (Swagger / OpenAPI) to classify every endpoint.
The Three Risks
- Shadow APIs — APIs seen in production traffic that don’t exist in your spec. These are undocumented endpoints that developers may have added as debug hooks, quick fixes, or simply forgotten to document. They’re a significant risk because no one is actively monitoring or securing them.
- Zombie APIs — Deprecated APIs (marked as such in your spec, e.g., a V1 endpoint you’ve replaced with V2) that are still getting called in production. These often carry old vulnerabilities and should be decommissioned.
- Orphan APIs — APIs in your spec that haven’t been seen in production for an extended period. They may have been removed from code but never removed from documentation — leaving a misleading security surface.

In a single scan, 378 shadow APIs surfaced — undocumented endpoints actively running in production with no visibility or controls
Working with API Specs
AccuKnox supports two paths:
- You have a Swagger/OpenAPI document — upload it and run a scan against your live traffic to immediately get shadow/zombie/orphan findings.
- You don’t have one — AccuKnox can generate an OpenAPI spec from observed traffic, per collection. Your dev team can use it to bootstrap or update documentation.

One click generates a downloadable OpenAPI specification from real traffic observed on any collection.

Upload your existing Swagger doc and select which collections to scan — AccuKnox does the rest.

The generated spec captures full request body structure — including sensitive fields like credit card numbers that were detected in live traffic.
To mitigate these risks effectively, developers often use specialized testing tools. You can check out our guide on the top 10 API security testing tools for OWASP compliance to see how to automate this validation.
Part 3: Filtering, Response Codes & Prioritization
The API inventory can be enormous. AccuKnox is built to help you prioritize what matters:
- Filter by sensitive parameters — show only endpoints that touch PII, PHI, or credit card data
- Filter by access type — authenticated vs. unauthenticated, internal vs. external
- Filter by response status code — instantly see which endpoints are throwing 401s, 403s, 404s, 500s, 503s

Filter your entire API inventory by response code to instantly surface failing, unauthorized, or anomalous endpoints.
For a deeper dive into the technical mechanics of these filters, refer to our official API security documentation.
Part 4: What’s Available Now vs. What’s Coming
Available now:
- Full API discovery and inventory (north-south + east-west)
- PII/PHI detection in request/response bodies and headers
- Shadow, zombie, and orphan API classification
- API spec generation and upload
- Findings lifecycle with workflow automation (e.g., auto-create a Jira ticket when a new shadow API appears)
- Connectors for all major gateways — cloud, on-prem, Kubernetes
- API static scanning (DAST)
- On-prem and air-gapped deployment support
Coming soon:
- Rate limiting and policy controls (currently in dev testing)
- Full OWASP API Security Top 10 coverage
- Compliance reporting mapped to API security controls (SOC 2, ISO, etc.)
How AccuKnox API Security Pricing Works
Licensing is based on number of unique API endpoints — not traffic volume. If an endpoint is called a million times a day, it still counts as one endpoint. A rough sizing rule: divide your total endpoint count by 50 to get your unit count.
This keeps pricing predictable regardless of traffic spikes — a deliberate choice over ingestion-based models, which scale with volume and can be hard to forecast.
The Bottom Line
API security is a crowded space. AccuKnox’s differentiation comes down to two things:
- Platform depth — API observability sits alongside file, process, and network observability in a single platform. When you’re investigating an incident, you can correlate what an API was doing with what process was executing and what network connections were open. Most standalone API security vendors can’t do that.
- Deployment flexibility — cloud, on-prem, Kubernetes, air-gapped. Many SaaS-first competitors can’t match this, which matters significantly in enterprise and regulated environments.
If your primary need right now is visibility — seeing what APIs exist, which are risky, and which are undocumented — AccuKnox covers that well today. For a high-level summary of these capabilities, you can download our API Security Solution Brief (PDF).
Have questions about a specific deployment scenario or integration? Read our foundational guide on the importance of API security or Book a Demo to get personalized guidance on how you can secure and get full visibility into your API collections and endpoints today.

Get a LIVE Tour
Ready For A Personalized Security Assessment?
“Choosing AccuKnox was driven by opensource KubeArmor’s novel use of eBPF and LSM technologies, delivering runtime security”

Golan Ben-Oni
Chief Information Officer
“At Prudent, we advocate for a comprehensive end-to-end methodology in application and cloud security. AccuKnox excelled in all areas in our in depth evaluation.”

Manoj Kern
CIO
“Tible is committed to delivering comprehensive security, compliance, and governance for all of its stakeholders.”

Merijn Boom
Managing Director



















